New details on how Russian hackers may have infiltrated American computer systems
We are getting a better idea of how Russian hackers may have infiltrated American computer systems -- and how they covered their tracks.
U.S. intelligence agencies believe Russian hacking units often use other people’s computer networks to “hide their malicious actvity.”
Newly-declassified documents show that U.S. investigators suspect that Russian intelligence services have access to compromised computer infrastructure in as many as 60 countries.
According to this joint analysis, U.S. intelligence agencies have been tracking specific Russian signatures or fingerprints of malicious cyber activity for years which led them to focus on one culprit in connection with the cyberattack that affected Democratic party officials.
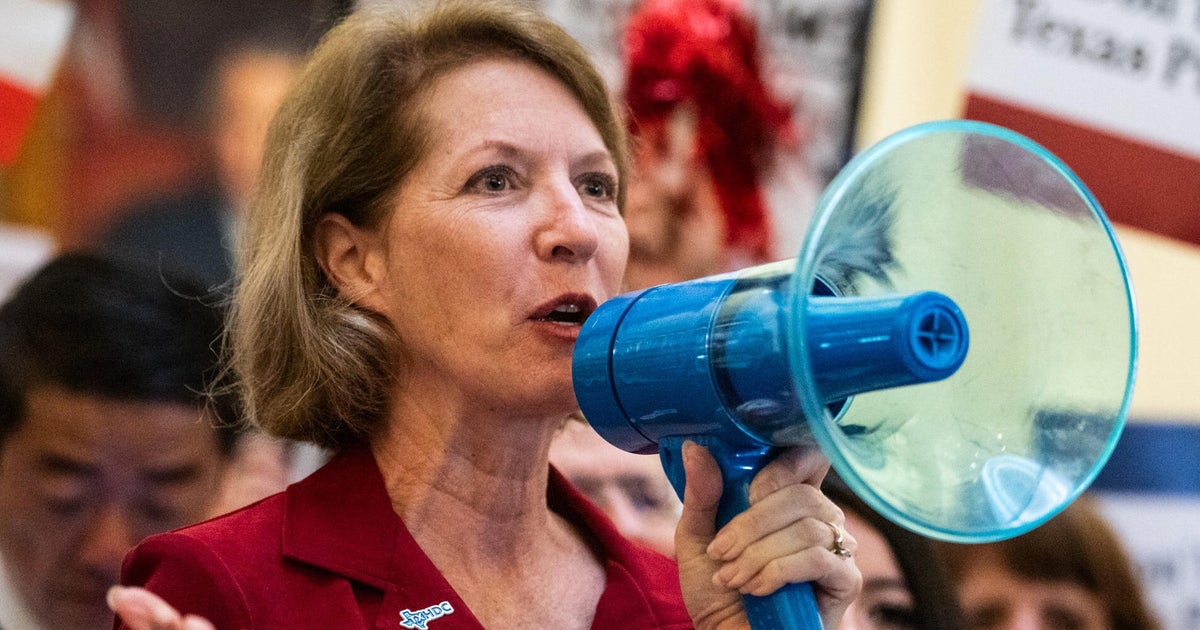
“It was very clear from Day One that this was Russia,” says Kelly Ward, the executive director of the Democratic Congressional Campaign Committee.
Ward says she and other senior Democratic party officials were notified of the cyberattack on June 14th. But by then it was too late. The hackers had already stolen valuable opposition research for Congressional races and the information was about to show up in Republican ads.
“The material that was leaked was weaponized in a way to affect our most important races at the most important times,” Ward says. “The hackers released the materials and put them on the internet.”
Cybersecurity experts and U.S. officials say the tactic is classic Russian information warfare and it has been used in countries around the world including Ukraine and Turkey. Investigators say with the blessing of Vladimir Putin, Russian intelligence services have worked to develop a playbook of cyber espionage which calls for elaborately planned cyberattacks to leak embarrassing documents or cause other disruptions.
President Obama has ordered a report on the Russian cyberattacks and it is expected to be completed sometime in the next few weeks. U.S. officials tell CBS News that through a combination of forensic evidence and human intelligence, it will reveal new details about the cyberattacks that have yet to come to light.