Hacking techniques used against DNC, Podesta also targeted journalists covering Russia
Debris was scattered for miles when the Malaysia Airlines Flight 17 was shot down over Ukraine in 2014. All 298 on board were killed.
The investigative website called Bellingcat was among the first to conclude that Russian separatists fired the missile, and that’s when the group landed squarely in the crosshairs of Russian hackers.
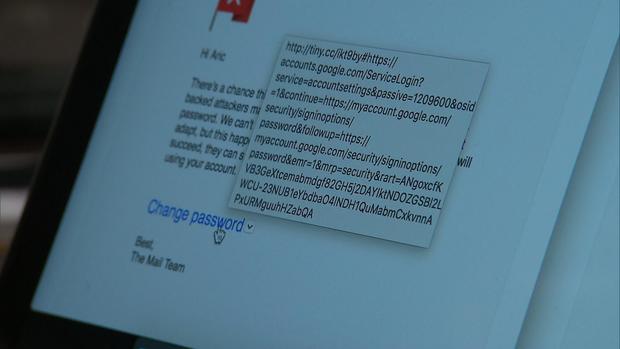
“You see these fake emails and they look they’re from Google or whatever. You click them and they steal your information,” said Aric Toler, one of Bellingcat’s investigators.
It’s called spear phishing, and he said it’s how the Russians attacked Bellingcat.
The emails look totally legitimate, but there are a few ways a user can tell they are not.
What should be a short link instead contains hundreds of characters.
“Put in your password and boom, they got you,” Toler said.
Fearing a trap, he sent the suspect emails to ThreatConnect, one of the top cybersecurity teams in the U.S.
They discovered that the Russian hacking group “Fancy Bear” had used the same spear phishing technique against Bellingcat that was used against the DNC and Hillary Clinton’s campaign chair John Podesta. Many of the hacks used the same email service in Moscow.
U.S. investigators agree the series of hacks originated in Russia, but less clear is whether the cyber attacks were approved by the Kremlin after the fact, or part of an orchestrated campaign.
Bellingcat’s contributor in Moscow, Ruslan Leviev, believes the Kremlin directed the attacks.
“I started receiving phone calls, death threats,” he said.
After his reports exposed government deception, Leviev’s online accounts were hacked, his passport, personal photographs and home phone number all posted online.
The attackers not only hacked his computer, but they also bypassed his security backup by hijacking his cellphone as well.
He said that only Russia’s Secret Service has that kind of capability.
“Sometimes I am worried about my safety, but it’s our life. We must battle for our future,” he said.
“We don’t have another choice.”