The phishing email that hacked the account of John Podesta
March 2016
This appears to be the phishing email that hacked Clinton campaign chairman John Podesta’s Gmail account. Further, The Clinton campaign’s own computer help desk thought it was real email sent by Google, even though the email address had a suspicious “googlemail.com” extension.
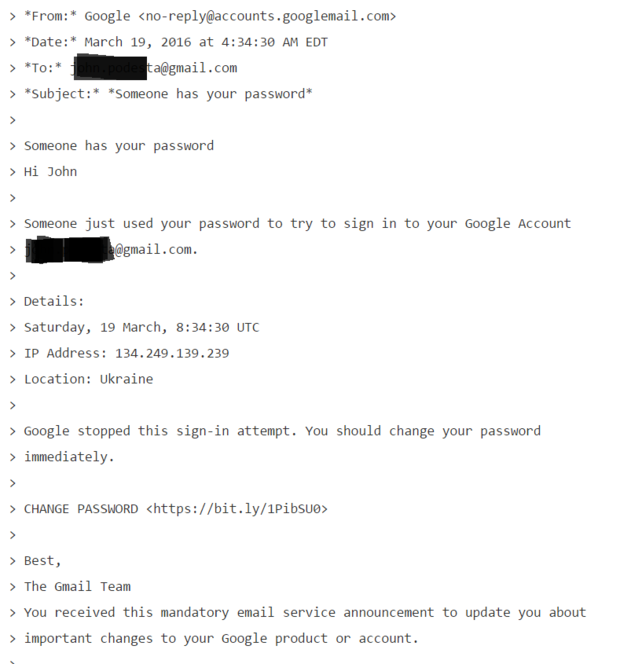
The email, with the subject line “*Someone has your password,*” greeted Podesta, “Hi John” and then said, “Someone just used your password to try to sign into your Google Account john.podesta@gmail.com.” Then it offered a time stamp and an IP address in “Location: Ukraine.”
“Google stopped this sign-in attempt. You should change your password immediately.” And it then offered a link to change his password.
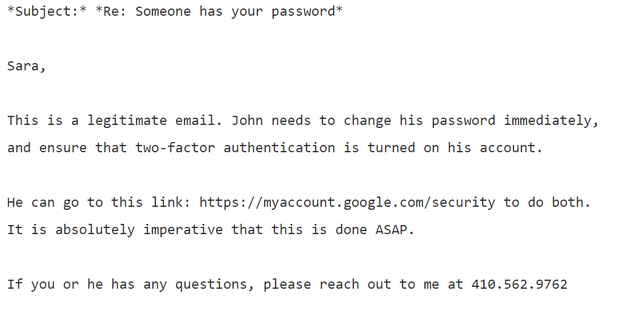
“This is a legitimate email,” Charles Delevan at the HFA help desk wrote to Podesta’s chief of staff, Sara Latham. “John needs to change his password immediately, and ensure that two-factor authentication is turned on his account.”
Delevan included the Gmail link that would be used to change a user’s password, but whoever changed Podesta’s password instead clicked on the shortened URL that was in the original phishing email. This is the same technique used to hack Colin Powell’s emails and the Democratic National Committee emails, according to the website Motherboard.
All of these hacks were executed using these shortened URLs in fake emails, according to Motherboard, and those URLs “were created with a Bitly account linked to a domain under the control of Fancy Bear,” a group of Russian hackers.
In October, WikiLeaks began releasing thousands of Podesta’s emails daily before the November presidential election.