Report: Android phones vulnerable to data attack
Most of the Android smartphones on the market are susceptible to an attack in which someone could access calendar and contact data over an unencrypted Wi-Fi network, a team of German researchers said in a new report.
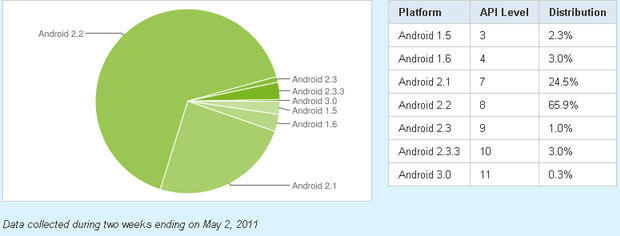
The problem is fixed in the latest version of Android, but 99.7 percent of all Android devices are running older versions, they said. Attacks can be carried out over unencrypted Wi-Fi hotspots by an attacker sniffing an authentication token (authToken) used by the Android devices when they communicate with the Google services, according to "Catching AuthTokens in the Wild: The Insecurity of Google's ClientLogin Protocol," which was released last Friday.
It is "quite easy" to launch an impersonation attack against Google Calendar, Contacts, and Picasa Web albums on newer Androids, and theoretically all Google services using the ClientLogin authentication protocol for access to its data APIs (application programming interfaces), the report said.
A Google spokesperson confirmed that the latest version of Android, 2.3.4 for smartphones, and 3.0 for tablets does not have the problem. The company is looking into the Picasa issue, he confirmed.
Here's how it works. With the ClientLogin Protocol, applications request an authToken from the Google service by sending an account name and password via an https (hypertext transfer protocol secure) connection. The authToken is valid for up to two weeks and is used for subsequent requests to the Google service API. If the authToken is sent over unencrypted http, an attacker could use network sniffing software, like Wireshark, to grab it, the researchers said.
"For instance, the adversary can gain full access to the calendar, contacts information, or private web albums of the respective Google user," they wrote. "This means that the adversary can view, modify or delete any contacts, calendar events, or private pictures. This is not limited to items currently being synced but affects all items of that users."
An attacker could grab multiple authTokens by setting up a Wi-Fi access point with the same name of a common wireless network provider, such as T-Mobile, Starbucks or attwifi and wait for Android phones with default settings to automatically connect to a previously known network and start syncing immediately, according to the report. Syncing would fail, but the attacker could capture authTokens for each service that attempted to sync.
Not only does this put the Google user data at risk, but that of all the contacts on the device. An attacker also could change the stored e-mail addresses of contacts and the Google user would be at risk then of inadvertently sending sensitive information to the attacker instead of the intended recipient, the researchers noted.
"We tested this attack with Android versions 2.1 (Nexus One), 2.2 (HTC Desire, Nexus One), 2.2.1 (HTC Incredible S), 2.3.3 (Nexus One), 2.3.4 (HTC Desire, Nexus One), and 3.0 (Motorola XOOM) and with the native Google Calendar, Google Contacts, and Gallery apps (or respective synchronization services)," the report said.
Calendar and Contacts apps transmit requests in clear text via http up to Android 2.3.3 and are therefore vulnerable to this type of attack. Since Android 2.3 the Gallery app provides Picasa Web Albums synchronization, which is also not encrypted, the researchers said. In Android 2.3.4 the Calendar and Contacts apps began using an https connection, however the Picasa sync does not, they said.
Android users should update to Android 2.3.4 as soon as possible. "However, depending on your phone vendor you may have to wait weeks/months before an update is available for your phone," the researchers wrote.
Also, Android users should switch off automatic synchronization in the settings menu when connecting with open Wi-Fi networks and avoid using open Wi-Fi networks at all when using the apps.