How strangers can hack the phone in your pocket
“In today’s world, there’s really only two types of companies or two types of people which are those who have been hacked and realize it and those who have been hacked and haven’t.” That’s what mobile security expert John Hering tells 60 Minutes correspondent Sharyn Alfonsi about the danger of cellphone hacking on this week’s broadcast.
While most people worry about their computers getting hacked, Hering explains that phones are vulnerable, too. To prove his point, Hering assembled a group of ace hackers at a Las Vegas hotel where the 60 Minutes team was staying. In the video above, 60 Minutes Overtime explores what happened.
The hackers Hering gathered, all of whom try to identify security weak spots in order to protect the public, were in Las Vegas for Defcon, a conference that draws roughly 20,000 hackers each year to trade secrets and share information.
60 Minutes producer Howard Rosenberg asked them to share some of their tricks. “We worked on this story for well over two years and during that period of time, we were constantly challenging the hackers to take it to another level and to demonstrate for us what they claimed,” he tells 60 Minutes Overtime editor Ann Silvio. “They say, ‘Everything is hackable.’ And we kept saying to them, ‘OK, prove it.’”
And prove it they did. One hacker, Jon Oberheide, showed 60 Minutes an app he created that looks legitimate but allows him to take control of a phone and suck out its information. He demonstrated for Alfonsi how he could instantly pull up her contacts, recent purchases and text messages. “It’s almost uncanny to watch how creative these folks are,” says Rosenberg.
Another hacker, Adam Laurie, uses radio frequency identification to hack phones. “So the way this hack worked -- he didn’t need my phone number,” Alfonsi explains. “All he had to do was physically touch my phone.” He demonstrated by brushing by her in the lobby of her hotel. When he did, he used a special hand-held device to push a credential across to her phone so it trusted his Bluetooth and actually dialed Laurie, allowing him to listen in on anything discussed in the room with Alfonsi’s phone.
If all of this sounds creepy, there are ways to protect yourself, Rosenberg explains. A so-called “CryptoPhone,” developed by a German company called GSMK, allows users to have encrypted conversations. It also alerts the user when someone is trying to attack or hack into his or her phone.
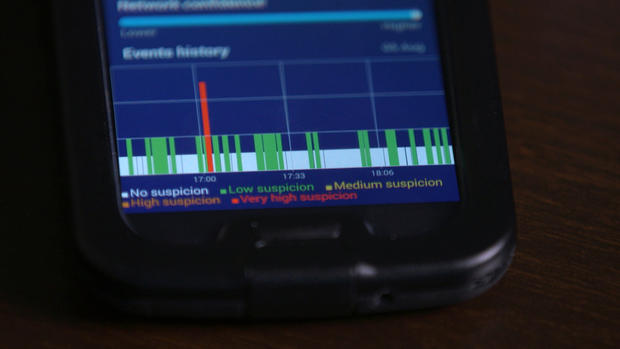
“Certain government facilities will try to get into your phone if you get too close to them,” Alfonsi explains. To demonstrate, Les Goldsmith, CEO of ESD America, a company that specializes in countersurveillance technologies, took Alfonsi for a ride through the desert near a secure government facility. As they were driving past, a red line appeared on the CryptoPhone, indicating that her privacy was compromised. If she were using a regular phone, the government agency could hear her call and read her text messages.
But CryptoPhones aren’t realistic for average consumers, Rosenberg says. They carry a price tag of around $3,000 each, and both parties on the line must be using CryptoPhones to achieve a secure conversation.
So what are we regular-phone carrying folks to do? “I’d say, the average person is not going to be exposed to the type of attacks we showed you today,” Hering says on 60 Minutes. “But our goal was to show what’s possible. So people can really understand if we don’t address security issues, what the state of the world will be.”
Rosenberg agrees. “We’re not trying to scare people, far from it,” he says. “We’re trying to raise consciousness and as the world migrates to mobile devices, what the hackers call the attack surface grows larger and larger and larger.”
The video above was originally published on April 17, 2016 and produced by Ann Silvio and Lisa Orlando; it was edited by Lisa Orlando and Will Croxton.